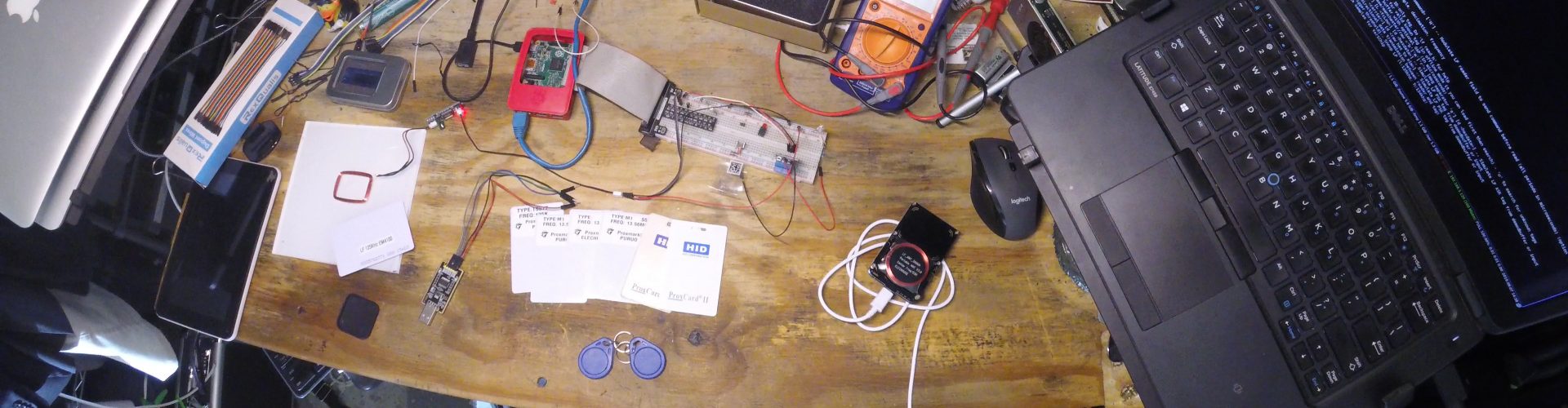
Going through my collection of random circuit boards I came across a 125KHz RFID reader that I had forgotten about, so I started playing with it.
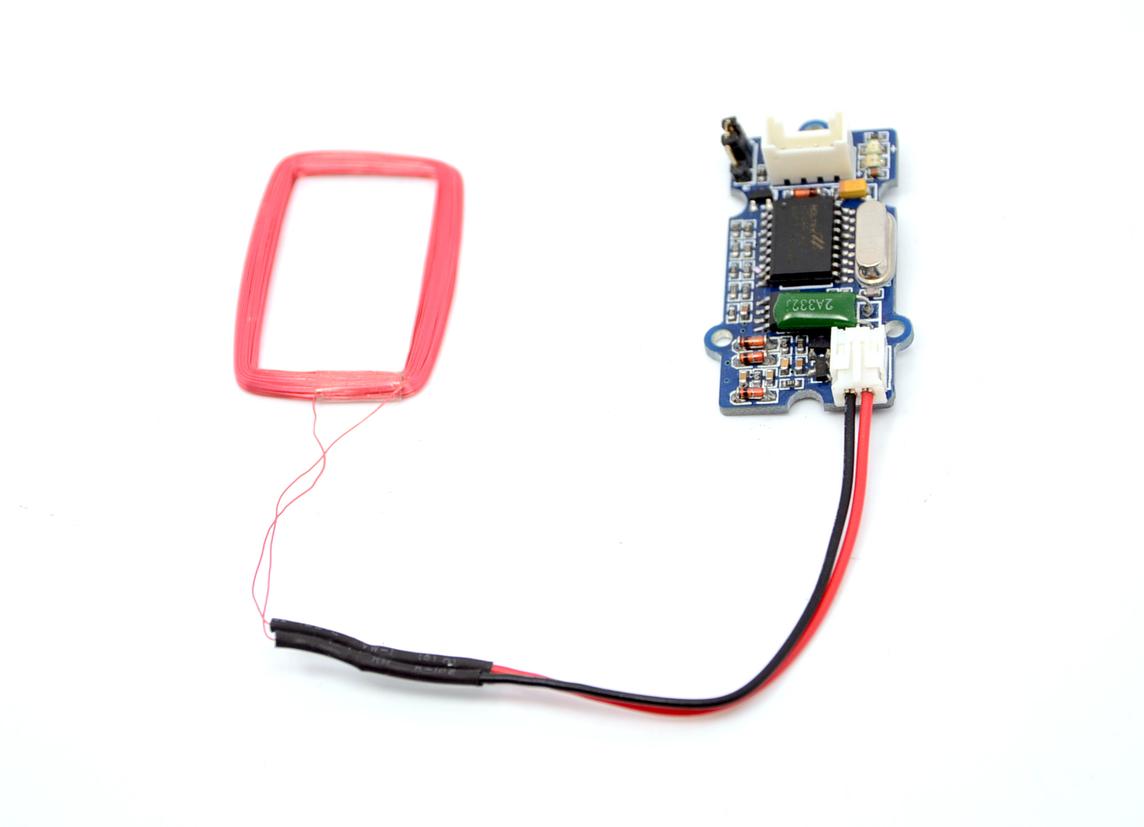
At first I wired it into one of my FT232 adapters and was able to pull the ID from the test card that it came with. From there I wired the reader board into a Raspberry PI, then wrote a short python script to toggle a relay when the card is read. That code is on Github.
Once I had reached the limitations of this simple reader and watched numerous DEFCON/BlackHat talks about RFID hacking, I purchased the almighty ProxMark3.

With this in hand I was able to scan the test key card from the first reader, as well as all the keycards I could find in my house, including HID cards.
Getting the software running wasn’t too bad, but also wasn’t a simple ‘apt install’ and run it. Some compilation was needed, and I had to update the bootloader along with the firmware itself, but that wasn’t too bad. Just follow the great instructions here (I am running Kali, other guides are available there as well so find what you need).
While the ProxMark3 can make duplicates, it can also emulate the last card scanned, so there isn’t even a need to carry blanks.
A few noteworthy Github repos for this toy:
- Official ProxMark3 firmware
- Firmware modified to do LF/HID by default in stand alone mode
- Firmware modified to brute force RFID tags
Jumping way ahead for the moment, I’ve put together an idea.
More to come…